Using the API User Security Policy
Learn how the API User Security Policy is used to secure Community Manager administrator accounts.
For information about using policies in the context of the Community Manager developer portal, see Business Policies.
Table of Contents
Introduction
The "API User Security Policy" is the default security policy for Community Manager services and controls who can perform administrative actions on the Community Manager developer portal.
When a user installs the Akana Community Manager, Akana Community Manager APIs, and Akana Community Manager OAuth Provider features, a series of services specific to Community Manager are added to the "Services" folder of the Community Manager Tenants" organization located in Policy Manager. The API User Security Policy is automatically assigned to these services during the installation of the Community Manager features. You can select View References on the Actions Portlet of the Policy Details page to view services that the policy is attached to, and can also view the policy attachment on the Operational Policy Attachment Portlet of any of the Community Manager services.
Note: This service is for users that have installed the Akana Community Manager features.
In Community Manager, when you add an API using the Add a New API function, you automatically become API Administrator for that API. You can also invite individuals who you would like to give administrator privileges to your API via the Community Manager API > Admins interface. The API creator and approved administrators can access the API.
The "API User Security Policy" determines who the user is (administrator or standard user account). When a request comes to a Community Manager service, it is intercepted by the "API User Security Policy" before being processed. The policy checks to determine if the user is logged in, and whether the user is an administrator for the selected API or has a standard user account. Depending on the action, if the user is not authorized to perform the selected action, an error will be thrown or the option will be grayed out and not available for selection.
Configuration Options
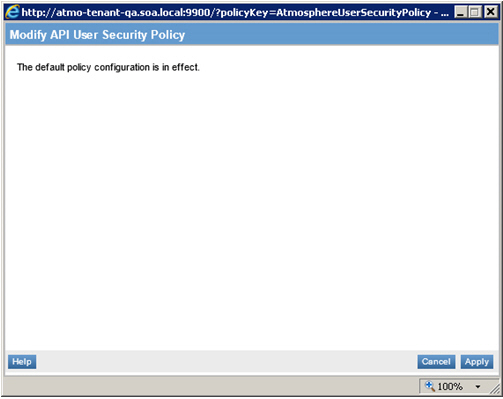
This policy type does not require any configuration. A default API User Security Policy is added to the Policy Manager Management Console as part of the Community Manager installation.
Configuration
Let's take a quick walkthrough of the API User Security Policy configuration process to get you started.
Step 1: Review Policy (in Policy Manager Management Console)
Verify that the API User Security Policy is present in the Policies folder of the Policy Manager root Organization as illustrated below. It should be added automatically as part of the Community Manager feature installation. The name assigned to the default policy is AtmosphereUserSecurityPolicy.
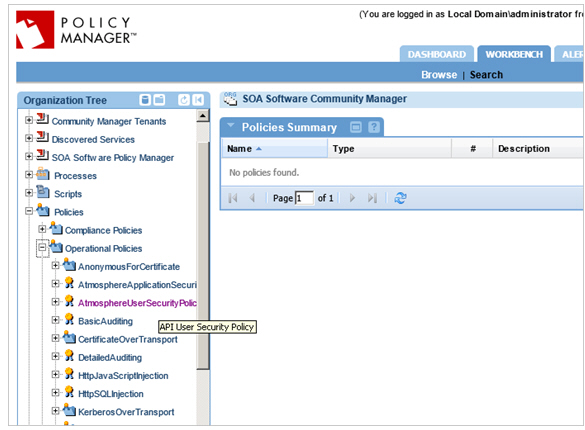
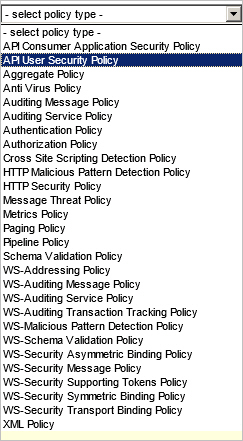
If the policy does not display, verify that you have correctly installed the Community Manager features. If you need an additional instance of the API User Security Policy to customize, use Add Policy to create one.
This policy type creates a policy with a default configuration that looks like the following:
Step 2: View Policy References and Attachments
You can view the services the default API User Security Policy is attached to by selecting View Policy References from the Actions Portlet on the Policy Details page.
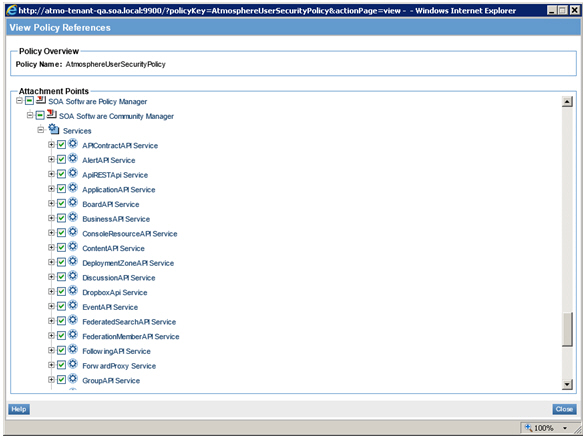
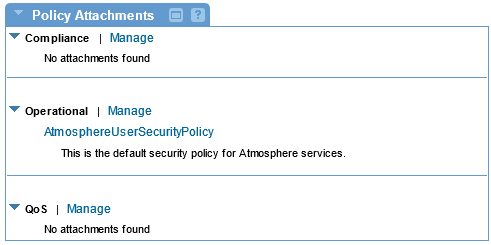
You can also view a policy attached to a service on the Policy Attachments Portlet in Akana Community Manager > Services > Service Details).
Activating a policy
When you create and configure a policy, the policy is in Draft state. When the policy configuration is complete, activate the policy: click Activate Policy and then confirm. See Activate a Policy.
A policy in Draft state is not available for general use. Once you activate the policy, it is in Active state and is available for use.
Attaching a policy
To use the policy, go to the Policies folder in the respective organization and attach the policy to a web service, binding, or binding operation.




